今天这篇将三者结合一下,也不要太复杂。有交换机有vlan,有防火墙有域策略,再加个NAT地址转换。
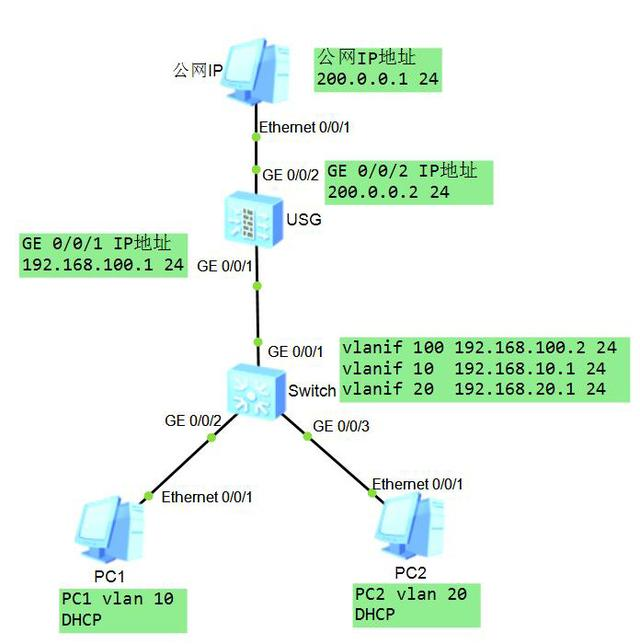
如上图,三层交换机S5700和防火墙USG5500对接,使用户PC1和PC2可以实现上网功能。交换机是三层交换机,可以完成跨网段数据转发。
配置思路:
1、交换机作为用户的网关,实现三层转发。同时作为DHCP服务器,为用户分配IP地址。
2、 防火墙通过NAT转换,使用户可以访问外网。
交换机Switch配置文件:
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]sysname Switch
[Switch]vlan batch 10 20
[Switch]int g0/0/2 //配置PC1相连端口
[Switch-GigabitEthernet0/0/2]port link-type access
[Switch-GigabitEthernet0/0/2]port default vlan 10
[Switch-GigabitEthernet0/0/2]quit
[Switch]int gigabitethernet0/0/3 //配置PC2连接端口
[Switch-GigabitEthernet0/0/3]port link-type access
[Switch-GigabitEthernet0/0/3]port default vlan 20
[Switch-GigabitEthernet0/0/3]quit
[Switch]int vlanif 10
[Switch-Vlanif10]ip address 192.168.10.1 24 //配置PC1网关
[Switch-Vlanif10]quit
[Switch]int Vlanif 20
[Switch-Vlanif20]ip address 192.168.20.1 24 //配置PC2网关
[Switch-Vlanif20]quit
[Switch]vlan batch 100
[Switch]int g0/0/1 //配置连接防火墙的接口和对应的VLANIF接口
[Switch-GigabitEthernet0/0/1]port link-type access
[Switch-GigabitEthernet0/0/1]port default vlan 100
[Switch-GigabitEthernet0/0/1]quit
[Switch]int vlanif 100
[Switch-Vlanif100]ip address 192.168.100.2 24
[Switch-Vlanif100]quit
[Switch]ip route-static 0.0.0.0 0.0.0.0 192.168.100.1 //配置缺省路由
[Switch]dhcp enable
[Switch]int vlanif 10
[Switch-Vlanif10]dhcp select int //使能DHCP服务
[Switch-Vlanif10]dhcp server dns-list 218.85.157.99 218.85.152.99 //自动分配的主从DNS服务器
[Switch-Vlanif10]quit
[Switch]int vlanif 20
[Switch-Vlanif20]dhcp select int
[Switch-Vlanif20]dhcp server dns-list 218.85.157.99 218.85.152.99
[Switch-Vlanif20]quit
防火墙USG配置文件:
<SRG>system-view
[SRG]sysname USG
[USG]interface g0/0/1
[USG-GigabitEthernet0/0/1]ip address 192.168.100.1 255.255.255.0 //配置连接交换机的接口对应的IP地址
[USG-GigabitEthernet0/0/1]quit
[USG]interface g0/0/2
[USG-GigabitEthernet0/0/2]ip address 200.0.0.2 255.255.255.0 //配置连接公网的接口对应的IP地址
[USG-GigabitEthernet0/0/2]quit
[USG]ip route-static 0.0.0.0 0.0.0.0 200.0.0.1 //配置缺省路由
[USG]ip route-static 192.168.0.0 255.255.0.0 192.168.100.2 //配置回城路由
[[USG]firewall zone trust //配置Trust可信任域并开启域间策略
[USG-zone-trust]add interface g0/0/1 //将防火墙的G0/0/1口加入Trust域
[USG-zone-trust]quit
[USG]firewall zone untrust //配置非可信任Untrust域并开启域间策略
[USG-zone-untrust]add interface g0/0/2 //将防火墙的G0/0/2口加入Untrust域
[USG-zone-untrust]quit
[USG]firewall packet-filter default permit all //开启所有域的域空间策略
Warning:Setting the default packet filtering to permit poses security risks. You
are advised to configure the security policy based on the actual data flows. Ar
e you sure you want to continue?[Y/N]y
[USG]nat address-group 1 200.0.0.2 200.0.0.2 //配置NAT地址池
[USG]nat-policy interzone trust untrust outbound
[USG-nat-policy-interzone-trust-untrust-outbound]policy 1
[USG-nat-policy-interzone-trust-untrust-outbound-1]policy source 192.168.0.0 0.0.255.255 //NAT转换对象是192.168.0.0网段的内网IP地址
[USG-nat-policy-interzone-trust-untrust-outbound-1]action source-nat
[USG-nat-policy-interzone-trust-untrust-outbound-1]address-group 1
[USG-nat-policy-interzone-trust-untrust-outbound-1]quit
[USG-nat-policy-interzone-trust-untrust-outbound]quit
测试结果
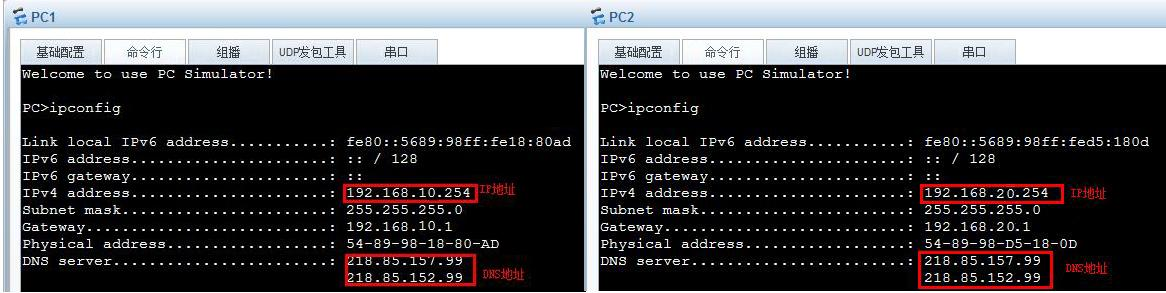
PC1与PC2成功DHCP到所在VLAN的IP和DNS地址
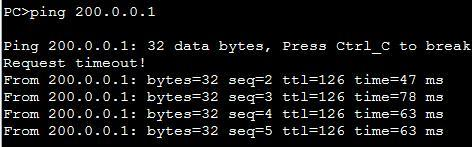
PC1PC2成功ping通公网PC